In today's increasingly virtual landscape, securing sensitive information is of paramount importance. To achieve this goal, organizations must deploy robust access control systems that effectively regulate user privileges. A well-designed system will mitigate the risk of unauthorized entry, thereby improving overall security posture. Implementi
 Brian Bonsall Then & Now!
Brian Bonsall Then & Now!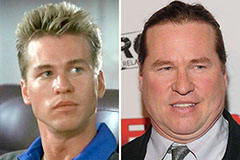 Val Kilmer Then & Now!
Val Kilmer Then & Now! Hailie Jade Scott Mathers Then & Now!
Hailie Jade Scott Mathers Then & Now! Raquel Welch Then & Now!
Raquel Welch Then & Now! Shannon Elizabeth Then & Now!
Shannon Elizabeth Then & Now!